- 1
- 2
Business e-mail compromise (BEC) is rapidly emerging as one of the most significant cyber threats facing businesses today. Although these scams have posed challenges for organizations for years, the rise of advanced...
Imagine arriving at work with your team, ready to take on the day's challenges, only for the Internet to suddenly go down. Emails stop functioning, and productivity comes to a standstill. What would you do? For many...
As tax season approaches, businesses are busy preparing financial documents, filing returns, and adhering to tight deadlines. Unfortunately, this hectic period presents an ideal opportunity for cybercriminals to...
Spring has arrived, signaling the perfect opportunity for a thorough clean-up. While you're busy decluttering your office and organizing your files, remember that your IT systems also need a refresh. A spring-clean...
As you navigate through the first quarter of 2025, it is evident that successful businesses are those that keep pace with the rapidly changing technology landscape. Reactive IT strategies, which involve addressing...
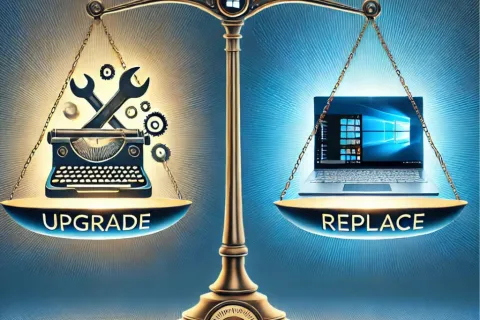
Windows 10 is approaching its end-of-life, with support concluding in October 2025. This puts businesses and individuals who still use the operating system at a crossroads. The key question is whether to upgrade...
It's time to declutter your digital life! National Clean Out Your Computer Day, observed on the second Monday of February, serves as a timely reminder to give your computer the care it needs. Just as a messy desk can...
It's game time - while the top football teams prepare for the biggest day in the sport, cybercriminals are strategizing for 2025. Just like in a championship game, combating hackers demands a solid strategy,...
Data Privacy Day on January 28 serves as a global reminder of the importance of safeguarding sensitive information. For business owners, data privacy is not merely a trendy term; it is essential for protecting their...